Introduction – Growth of IT-OT convergence in industrial verticals
As networks evolve and elements such as ultra-low latency and network dependency are in the center of this evolution, organizations are driving the initiative of automating processes through connectivity, IOT, artificial intelligence and machine learning. Verticals such as manufacturing, retail, mining, transportation, oil & gas, power & energy, among others, are driving intelligence in critical process and discrete flows, with the core objective of enhancing productivity, efficiency and reducing costs.
The key goal of attaining these objectives is to optimize the customer experience, while effecting growth and revenue enhancement. Organizations are thinking about different ways in which they interact with their target customers to provide an end-to-end, heightened experience in their journey, beyond the transactions. The imperative is to engage with customers to solve some of their most complex problems.
CX at the center of IT-OT convergence – Driving Growth and Revenues
Organizations across verticals are adopting connected IT-OT capabilities keeping in mind the following critical benefits that directly or indirectly impact customer experience:
- Receive and provide real-time information
- Optimize the use of the product/services
- Develop and build new products/services
We are seeing and experiencing an ever-growing convergence between vertical operations across the spectrum with applications, technologies and network connectivity. Organizations have been implementing connected technologies across the industrial process zone and at the same time integrating with the enterprise zone. Elements such as sensors, automated guided vehicles, programmable logic controllers, safety controls, SCADA, DCS, controllers, etc. are now being driven real-time through connectivity. Platformatization of solutions, coupled with I/IOT, machines learning and artificial intelligence, deep learning algorithms, data analytics, geofencing, and sensor fusion, industrial verticals are adapting to IT-OT technology environments to enhance and augment productivity, cost effectiveness and enriching offerings of products and services to customers.
The retail industry is a great example of the confluence of IT with operational technologies enhancing the customer experience, especially in today’s world, where the pandemic has instilled new norms for everything. Retailers are looking at enabling a shopping experience that moves from a touch-based experience to a completely zero-touch experience. This is being enabled with a series of several operational technology (OT) elements such as sensors, cameras, RFID tags, etc. integrated with intelligence-driven IT applications to generate data and analytics to boost a rich customer experience.
Increasing risk of cyber threats with expanding growth canvas
In the legacy environment, OT systems existed with air gaps while operating in their independent environment. However, with the convergence of IT-OT, we will see more and more operational technologies linked and integrated on connected networks. This convergence and integration of IT-OT creates a web-like machine-to-machine communication environment. This now expands the cyber-attack surface from the IT environment to the OT environment, making critical assets, processes and data vulnerable to rogue elements from a security standpoint.
Attack vectors in an IT-OT environment:
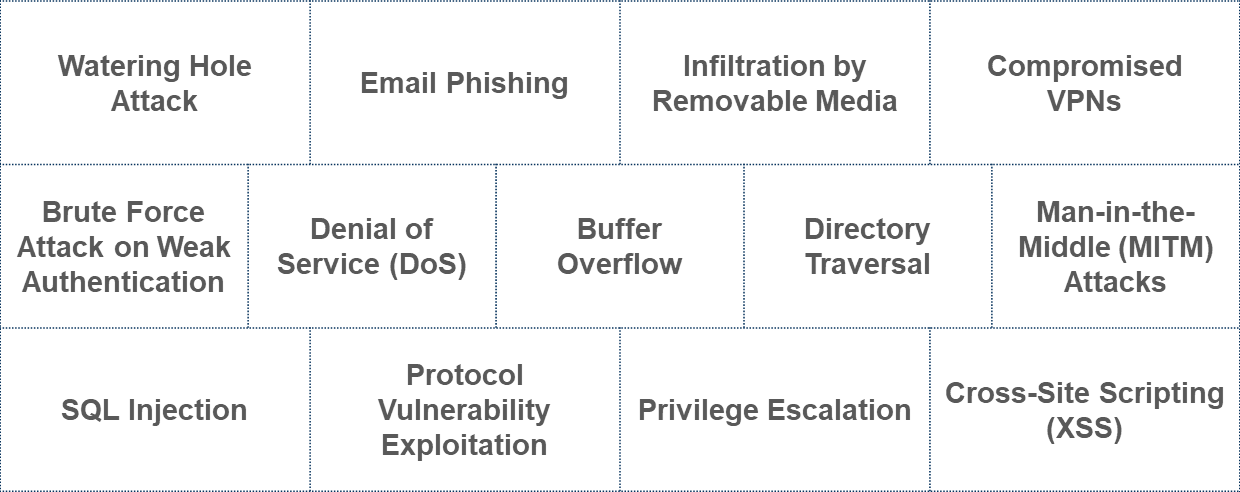
A cyber-attack on an OT environment can be more detrimental than that on the IT environment and can have far more serious effects. It doesn’t just expose sensitive customer data and information, but it also often results in extended unavailability of services and/or process continuation, ultimately resulting in extremely heavy financial losses – not only for the organizations in question, but also for their end-customers who may be impacted directly.
Addressing OT cybersecurity to protect and optimize CX
Organizations adopting the nascent IT-OT environment need to ensure protection from attack vectors by implementing comprehensive cybersecurity measures. Companies must drive compliance as per the NIST framework and guidelines of cybersecurity. NIST first released this framework in 2014, which was later updated in 2018 to expand on its applications, especially for risk management. This cybersecurity framework aims to maintain the reliable functioning of critical infrastructure, and is composed of five main categories – Identify, Protect, Detect, Respond, and Recover. Due to its robustness and comprehensiveness, many governments and organizations around the world have adopted this framework as part of their cybersecurity posture.
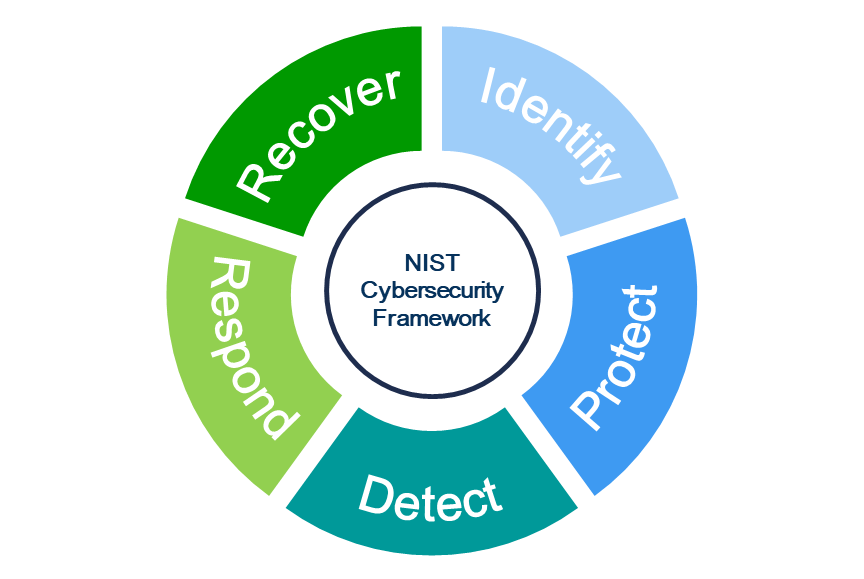
Based on the tenets of the NIST framework and guidelines, organizations must:
- Identify and assess – companies must use diagnostic capabilities to understand their assets based in the IT-OT environment and assess and analyze the gaps and the attack surface points that create threat vulnerability.
- Risk Analysis – companies must employ an effective diagnostic tool that will help them to score their current cybersecurity fitness and health. This will help organizations to make an acute risk analysis and thereby take the right steps to mitigate them.
- Multi-layered Security – on assessment of risks, companies need to design their cybersecurity requirements to comprehensively cover the entire environment. The layers of Applications, Networks and Devices must all be incorporated in the architecture and design. This exercise should pan across the extremely critical elements of People, Process and Technologies – based on current and future states.
- Testing & Assessment – it is crucial for organizations to test and assess their cybersecurity solution deployments. The solutions should effectively provide visibility to all the elements, predictively and intelligently identify the risks, respond proactively, and recover – all in real time.
Conclusion
The advent of IT-OT convergence promises to drive network connectivity and technologies to enhance productivity, cost effectiveness and intelligence with the integration of IOT, AI and ML. The ultimate benefits of these elements will be accrued by end customers of organizations in various verticals through an augmented customer experience. However, to deliver the highest level of CX, it should be a key imperative for organizations to stealthily protect the IT-OT environment at all levels of the architecture across the spectrum.
Samir Sakpal is the Director of Consulting, ICT, for the Americas at Frost & Sullivan. Samir has over 16 years of experience in management and strategy consulting, focused on clients in the ICT segment, and has worked extensively with telecom and technology customers. Samir has partnered as a trusted advisor to clients in devising and implementing winning strategies associated with crucial projects such as overall growth, go-to-market, product strategy, competitive strategy, etc. Samir continues to work with clients on innovative and next-generation technology, while helping them to map their growth in these areas.



